Top 40 Outstanding Cyber Security Companies In Singapore
- December 8, 2020
- Business Insights

Technology is becoming a progressively important part of the workforce throughout the past several decades. From email exchanges and banking transactions to business networking and collaborative working papers, companies depend on technology to always be linked and work efficiently. But, if challenged or even disrupted by these communication lines, it may have a catastrophic effect on the company. It’s not just big companies that need to think about cybersecurity.
Every company is never too tiny to have been a target of an assault on cybersecurity, it also happens to small to medium-sized enterprises. Hence, businesses are strongly encouraged to constantly update their cybersecurity with the latest technologies and software. There is no telling of when you will be invaded by malware or hacked. Thus, here are 40 cyber security companies in Singapore to help strengthen your company’s data protection.
Note: This list is strictly not in order.
1. GROUP8

As an active member of the global cybersecurity research alliance, GROUP8 is a key presence in Southeast Asia’s cybersecurity field. With a team of veteran cybersecurity experts backed by prominent artificial intelligence, GROUP8 offers an extensive suite of cybersecurity software to safeguard your company’s sensitive information and ensure you stay on top of any potential security threats.
GROUP8 is constantly innovating new systems to solve industry gap and ensure their clients’ assets stay secure. The company also strives to understand the threats every business faces so it can tailor its services to meet their needs. With GROUP8, you can rest easy knowing your business is protected from the latest cybersecurity threats.
Website: https://group8.co
Location: 12 Marina View #11-01, Asia Square Tower 2, Singapore 018961
Opening Hours: Mon-Fri 9AM-6PM | Closed on Sat & Sun
2. SEMNet
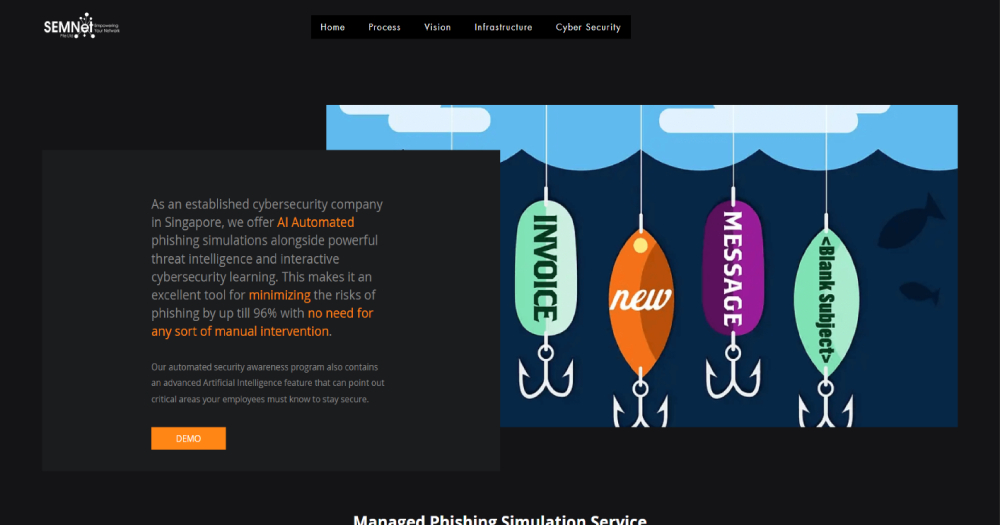
SEMNet has been in the industry for 14 years and has already served 120 satisfied customers, completed 310 projects, and sold 25 million products. Their talented cybersecurity professionals are passionate, talented, and dedicated to delivering exceptional customer service and helping you align your foals while making sure your company assets are protected. This company provides a comprehensive range of services including cyber security, infrastructure, AI Email security, automated phishing, automation and orchestration, cloud security, DDoS Protection, End point security, patching management, web vulnerability, and vulnerability management.
This cyber security consulting firm uses a proactive approach when investigating alerts and collecting security data from different sources. This means that it focuses on prevention instead of detection, which helps avoid threats before it even starts to form and cause damage.
Website: https://www.semnet.co/
Contact Number: +65 6356 9373 Fax: +65 6356 9374
Address: 28 Sin Ming Lane #02-132, Singapore 573972
Opening Hours: Mon – Fri: 9:00am to 6:00pm
3. Blackpanda

As the premier cyber security incident response group in Asia, Blackpanda is made up of elite special risk and security experts who have relevant backgrounds in intelligence, international special forces, law enforcement and forensics. Aside from Singapore, they are also positioned throughout the region to focus on cyber security incident response and digital forensics services to lead their clients through a crisis.
Their proprietary risk analysis and cyber security incident response software enables them to respond more efficiently and quickly, supported by their next-generation voice stress analysis technology, to both remove malware and internal human threats. With this team of experts, you can look forward to running your business without worrying about the constant threat of cyber-attacks, data breach and more.
Website: https://www.blackpanda.com/cyber-incident-response
Contact: +65 6692 9110
Location: 6 Raffles Quay, #11-07, Singapore 048580
4. MK Cybersecurity

Having served the IT industry for 8 years, MK Cybersecurity has grown to 30 “hackers” in both Singapore and Vietnam. With numerous experienced security researchers, vulnerability scanners, security certifications and best-practice methodologies, MK Cybersecurity provides vulnerability assessment and penetration testing to identify any security weakness in your website, mobile application and server.
While MK Cybersecurity has witnessed social transformation and technological advancement, their core values still remain the same as they strive to serve their clients better. To further assure the quality and honesty in their services, no service fee is required if there is no security issue found on the outcome of the security assessment.
Website: https://www.mkcybersecurity.com
Contact: +65 6707 3597
Location: Midview City, 18 Sin Ming Lane, #08-21, Singapore 573960
5. WebOrion
WebOrion Security Platform (WSP) is a series of key technologies that their security experts and developers have designed and constructed extensively throughout many years to provide the upcoming generation of cutting-edge technology to tackle the new cyber attacks. It consists of patent-pending elements such as our Material, Secure Replica Development Engines, Integrity and Image Analytics Engines, Machine Learning and Security Analytics Engines and High-Speed WAF Engines for the next generation. The WSP is designed to be efficient, interoperable and sufficiently versatile to incorporate API access points with third-party components.
Built on WSP’s core technical pillars, they created WebOrion Business and WebOrion Enterprise which serves various consumer sectors. WebOrion Enterprise has much more business-centric functionality including Roll-Based Access Control (RBAC), unified dashboards, SIEM integration, as well as on-premise characteristics. WebOrion Business provides a simple-to-use, scalable and accessible self-service platform for medium and small-sized enterprises.
Website: https://www.weborion.io
Contact: +65 9626 4242
Location: The Curie, 83 Science Park Drive, #02-01C, Singapore 118258
Opening Hours: Mon-Fri 9.15AM-6.15PM | Closed from Sat-Sun
6. i-Sprint Innovations

Established in 2000, Securing Identity and Cyber World Transactions is the leader in security-sensitive industries, requiring channel monitoring and quality data to improve user management. They enable individuals, organizations, and societies to build confidence and identity assurance to boost enormous productivity gain through digital identity and mobile security. i-Sprint Innovations offers state-of-the-art innovations to ensure secure access and data asset protection among the four major IT forces by integrating the newest technology in the most effective manner to boost confidence and certainty of identity.
They are conscious of the fact that in order to safeguard PINs as well as other sensitive information in terminal-host interaction, businesses might need to introduce end-to-end application-layer encryption for a secure environment. They provide a ‘E2EE’ solution to protect the data of applications that are sensitive to security like internet banking. Apart from this solution, another cyber security service that they provide is ‘Enterprise Access Control’. This solution can effectively address the complexity of managing your business applications and information assets with secure access.
Website: https://www.i-sprint.com
Contact: +65 6244 3900
Location: 750D Chai Chee Road, #08-01, Viva Business Park, Singapore 469004
Opening Hours: Mon-Fri 9AM-6PM | Closed from Sat-Sun
7. Cyber Security

With a tiger of a company like Horangi Cyber Security at your side, you can rest your fears surrounding cyber threats and attacks. The Singapore-based cyber security firm is made up of a global team of experts, who have been entrusted brands like Gojek, Fave, and NinjaVan. When you choose to rely on Horangi Cyber Security for your cyber security needs, your organisation will be covered by the latest product innovations and technology to thwart malicious online activities.
Firstly, they can evaluate and advise your organisation through their comprehensive Horangi Cybersecurity Assessment (CSA). This proprietary analysis method uncovers vulnerabilities and identifies challenges faced by your organisation so that a tailored game plan can be drawn up for your brand. Then, with their network of developers, engineers, security managers, and more, they can execute a long-term, actionable, and contextualised strategy to keep your organisation safe in the online realm.
Website: https://www.horangi.com/services/strategic/cyber-security-assessment
Contact: +65 3158 2031
Location: 109 North Bridge Rd, #05-21, Singapore 179097
Opening Hours: Mon-Fri 9AM-6PM | Closed on Sat & Sun
8. Connectivity Global

Connectivity Global is led by a team of local experts on IT infrastructure and solutions who have teamed up with a South Korean cybersecurity company. Utilising creative artificial intelligence (AI) technology, they design and sell their very own email security solutions. Having proven itself to be a leader in cybersecurity solutions, they’ve come up with their very own hero product, GUARD.
GUARD protects organisations from Business Email Compromise (BEC) attacks. A solution suitable for all types of firm, Connectivity Global has set their sights on becoming a global leader in cybersecurity with their innovative answers to safeguard customers from cyberattacks!
Website: https://www.c-globe.com/
Contact: info@c-globe.com
Location: Block 1015, Geylang East Avenue 3, Geylang Industrial Estate, #04-117, Singapore 389730
Opening Hours: 24 Hours
9. AdNovum

AdNovum is a high end software and security engineering since 1988. They are specialised in implementing technological projects that are demanding. Their alternatives fulfill the highest standards of quality. They are professionals in designing, implementing and maintaining solutions for software and safety that meet strict business and technical demands. A significant contributor to the achievement of the company is its solution-oriented engineering culture. Their corporate culture is defined by employee engagement.
Cyber security is often regarded as a contemporary organisation’s weakness. To avoid this, they guarantee that safety is prioritized for every solution they supply from the first day starting from their ideation and architectural design phases. As a result, security elements are carefully verified for a manufacturing setting at every step, from the execution phase to system settings. With AdNovum, they can assist you in conducting a cyber assessment to determine whether your company’s data is being protected. From there, you will receive complete clarity as to where your dangers lie and allow digital transformation to be safe and effective.
Website: https://www.adnovum.sg/en/offering/cyber_security.html
Contact: +65 6536 0668
Location: Shenton House, 3 Shenton Way, #23-03, Singapore 068805
Opening Hours: Mon-Fri 9AM-6PM | Closed from Sat-Sun
10. Tech Security

Tech Security is the pioneering IT, engineering and cybersecurity company in Singapore, with a team of dedicated, qualified and highly skilled cybersecurity experts who are committed to making the Web a safer place to do business. Through utilising their innovative A2F platform and cutting-edge IT Security services portfolio, they have effectively enhanced and protected digital resources from world-renowned multinational companies, government entities with essential national operations, and financial institutions that need the finest levels of protection and adherence.
They are proud to be a company with integrity and character. They are very serious about IT Safety and would like to insure that their customers are provided with the best information and bring it to the right audience in a state-of-the-art deliverable. At its heart, Tech Security is an online security company that provides high-quality anti-hacking products such as network security, vulnerability analysis, security screening of web apps, and much more to their clients through practical risk replication. They are not over-promising, they are delivering.
Website: https://techsecurity.com.sg
Location: Wintech Centre, 6 Ubi Road 1, #04-08, Singapore 408726
Opening Hours: Mon-Fri 9.30AM-6.30PM | Closed from Sat-Sun
11. Aon

They are the number one world skilled services firm providing a broad variety of retirement, risk and health solutions. Their huge amount of employees in more than hundred countries empower results for their customers by employing proprietary information and analytics to deliver insights that cut back volatility and increase performance. Aon acknowledged many years ago that their customers want services and products built around their unique requirements and provided in their industries and local markets by professionals with deep expertise.
They realised that globalisation demanded two things from them which are collecting the best ideas internationally and then delivering local solutions. Aon’s cyber security team has the ability to provide a precise analysis to help you make informed decisions about the optimum risk financing strategies of your organization. With Aon, you can understand the risks surrounding your company’s data, strengthen your security and be prepared for any situation.
Website: https://www.aon.com/singapore
Contact: +65 6221 8222
Location: SGX Centre, 12 Shenton Way, #26-01, Singapore 068804
Opening Hours: Mon-Fri 8.30AM-5.30PM | Closed from Sat-Sun
12. ITSEC Asia

Since its inception in 2004, it has been at the forefront of the information security industry. By securing their businesses, they empower their customers and aim to help the world run secure businesses. They have built their expertise on over a decade of industry-wide experience in providing cutting-edge information security services and solutions, and this knowledge underpins their determination to provide futuristic services. ITSEC partner with businesses, providing them with an integrated portfolio of information security services and solutions that encompass a corporate value chain.
ITSEC Asia offers ‘Database Security Assessment’ which is a customized area of information security in the wider field. It deals with a wide range of information security controls to safeguard database systems, database applications, including data, database servers, and accompanying network links, from nondisclosure and accountability compromises. While many organizations acknowledge the significance of safety of data, many of them don’t have appropriate data base safety measures in place. This may expose them to different kinds of hazards.
Website: https://www.itsec.asia/application-security.html
Contact: +65 3159 1145
Location: 71 Robinson Road, #14-01, Singapore 068895
13. Proofpoint

Stop dangers from email and cloud, along with malicious software, phishing credentials, and email fraud. They assist you to prevent consumers from encrypting your database for fraud and other assaults. Resolve threats more effectively and efficiently even when they’ve been delivered with forensic linguistics-enriched warnings, computerised workflow and arrangement. Protect your most confidential data and adhere with the ever-evolving legislation without the headaches and costs of legacy data protection tools.
They assist you to gather, archive, monitor and handle protected data sent through email via transparent, computerized encryption. Recognize where your most sensitive information lives and handle it in a manner that is compatible with the law. Prevent the exposure of data and improper data access in cloud applications that regulate who or what applications have access to it. Minimize successful spoofing and malicious software attacks by enabling your people to spot and report dangerous emails and by securing their digital personal activity. You will be able to achieve all these with Proofpoint.
Website: https://www.proofpoint.com
Contact: +65 6559 6128
Location: Beach Centre, 15 Beach Road Level 3, Singapore 189677
Opening Hours: Mon-Fri 9AM-6PM | Closed from Sat-Sun
14. Tenable

Image Credit: TenableA decade ago, as the creator of Nessus, which is now the most commonly deployed IT vulnerability evaluation solution, Tenable started the IT Vulnerability Management industry. Given the increasing severity and frequency of cyber assaults frequently occurring owing to an absence of fundamental cyber hygiene, it has never been more essential to evaluate IT equipment for problems.
Just as they pioneered the IT Vulnerability Management industry, Tenable is once again at the forefront of innovation in this new age to secure the developing Cyber Exposure market’s contemporary digital enterprise. Tenable.io, the very first cybersecurity visibility platform around the globe, it supplies protection with the opportunity for any company to see their whole cyberattack surface any given period, from OT to internet-of-thing to cloud to IT, and gives an insight to the CISO, C-suite and Board members to concentrate on the most crucial issues and create better strategic choices.
Website: https://www.tenable.com
Contact: +65 3159 0836
Location: Parkview Square, 600 North Bridge Road, #11-06/07/08, Singapore 188778
Opening Hours: Mon-Fri 9AM-5PM | Closed from Sat-Sun
15. Soverus

In order to provide risk and security consultancy services, Soverus was founded in the year 2008, in April. A new executive group took over the company’s operations in Feb, in the year 2010, extending its services which include Security Guarding, Security Consultancy, Security Systems, Cyber-Security, Big-data Analytics, Private Investigations and IT Forensics. With the specific needs of customers as their focus Soverus Consultancy has managed to secure essential infrastructure across markets. Their main objective is to provide protection to customers and the larger community in Singapore and abroad.
Be it Defense Master Planning and Development, they are proud and determined to take charge of all of your security requirements. Soverus Consultancy provides the most efficient tactical security solutions by recognizing the customer’s complex needs. Soverus is a leading cybersecurity software company that provides protection for people and property through innovative business products and solutions customized to the needs of an individual or a business. They include a comprehensive range of software solutions and services and bring their own skilled in-house services as well as other leading brands. They do provide turnkey solutions and facilities for maintenance.
Website: https://www.soverus.com.sg/joomla/services/166-cyber-security1
Contact: +65 6813 9500
Location: 38 Alexandra Terrace, Singapore 119932
Opening Hours: Mon-Fri 8.30AM-6PM | Closed from Sat-Sun
16. F-Secure

F-Secure has evolved into a credible cyber security leader from its humble beginnings more than thirty years ago, gaining the confidence of organisations and individuals around the globe. They hire the industry’s brightest minds while retaining a relentless focus on developing cyber safety pros in the next generation. Their experts are constantly disrupting the industry. Their research-led strategy, victories in contest hacking, and conference talks are gaining worldwide recognition. The portfolio of F-Secure was based on a desire to be first.
They have developed a passion for taking on the most powerful cyber threats in the world from three centuries of experience preventing sophisticated cyber attacks. The biggest, most robust endpoint security solution in the industry is the F-Secure Protection Service for Business. It is intended to solve complex business security requirements from the ground up, without excessive overhead management or maintenance. It safeguards all your gadgets from attacks, such as malware and breaches of data. And it provides security for a range of cloud systems for Mac and Windows laptops, android and ios devices.
Website: https://www.f-secure.com
Contact: +65 6221 0725
Location: 158 Cecil Street, #04-01, Singapore 069545
Opening Hours: Mon-Fri 9AM-5.30PM | Closed from Sat-Sun
17. Apvera

Apvera is all about providing cyber security solutions that are over and above the current state of affairs. Conventional rim-based safety is not sufficient nor are its alternatives when it comes to ensuring the safety of your company’s data. In order to semantically predict and analyze danger in relation to norms and frameworks, a precursor to modern cyber security risk management has a profound knowledge of the general threat landscape within the organisation and analytical instruments. In order to contextually predict and view risk in accordance with guidelines and protocols, a prerequisite to effective cybersecurity risk management has a thorough understanding of the broader threat environment within and its analytical tools.
Apvera Insight360 optimizes cyber warfare capabilities by first examining through a range of network and endpoint detectors during the most comprehensive set of information sources gathered. This automatically detects end-users and apps and categorizes information based on their importance, quality, and criticality level when assessing data protection baseline for security controls. Apvera Insight360 implements context-aware machine learning frameworks and algorithms across all consumer, system and application activity dimensions, producing accurate abnormal incidents and patterns. Ultimately, it offers regulatory framework and industry standard compliance perspectives that are developed and that distil the current cyber information into actionable information.
Website: https://www.apvera.com
Contact: +65 3158 8697
Location: 20 Maxwell Road, #09-17, Singapore 069113
Opening Hours: Mon-Fri 9AM-6PM | Closed from Sat-Sun
18. PCS Security

Company data for any corporation have always been an important asset. It might be details about clients, business contracts, brand designs, and much more. When technology progresses and storage becomes more available, for faster recovery and evaluation, more and more data is stored online. Slipped into the hands of the wrong people either through unauthorised access or unintentional disclosure, this can cause serious damage or humiliation to an individual or body of government. Associations, therefore, need to take security precautions to protect their crucial data and information from unauthorised access, be it vindictive or unintentional, in order to safeguard their competitive edge.
One way of protecting data is by using data protection and authentication methods. PCS Security has experience in data protection and offers a variety of data protection and authentication solutions to meet clients ‘ security requirements. Enhanced authentication key management software which encrypts and secures confidential information using an automated system. This effectively allows a company to track and analyze their encrypted use of data and to practice prompt revocation of access to their information-intensive sector. It provides simple, real-time access control data encryption technology.
Website: http://www.pcs-security.com
Contact: +65 6692 7000
Location: Tampines9 Building, 9 Tampines Street 92, Singapore 528871
Opening Hours: Mon-Fri 8.30AM-6PM | Closed from Sat-Sun
19. NEX CorporateIT

With the introduction of digital technology leading to increased efficiency and reduced overheads among other advantages, it is not possible to overstate the dangers of a possible security breach from implementing a remote management strategy. However, it shouldn’t be at the cost of functionality and efficiency to try a protection for remote access. NEX CorporateIT is specialized in designing active wireless networking systems that combine protection of the network layer and management of mobile devices.
Effectively, their programs prevent potential data attacks and other expensive complications. Their purpose is to help their customers take advantage of corporate flexibility while minimizing the associated risks. Their biggest motivation comes from their capacity to deliver peace of mind with the services their clients need from their company. You can depend on them for a strong defense for the communication network of your company. They are pleased to say that their strategies have been generally successful in removing all threats to their clients ‘ safety.
Website: https://www.nexcorporateit.com
Contact: +65 6653 3368
Location: 7000 Ang Mo Kio Avenue 7, Singapore 569877
Opening Hours: 8AM-8PM Daily
20. Sixscape Communications

Sixscape Communications is a cryptographic encryption and communication provider headquartered in Singapore focusing on protection based on digital certificates. Sixscape Communications brings digital identification and interactions to the next level as the world welcomes digital convergence, IoT, the need for password-less authentication and genuine end-to-end encryption of channels of communication. In addition to the use of modern and complementary technology paradigms, they protect all encryption and communication networks including fax, talk, internet, applications and audio/video, in addition to reframing protection for IoT nodes and traffic between them.
Sixscape Communications protection includes strong encryption, secure communication via encrypted email, document signing, secure file transfer, secure chat, web device and web authentication without passwords. Through installing electronic certificates on each end of the link, it is essentially possible to obtain end-to-end direct and encrypted interaction between two entities without intermediary servers, which is a first in the industry.
Website: https://sixscape.com
Contact: +65 6509 8070
Location: Vertex Tower B, 33 Ubi Avenue 3, #08-26, Singapore 408868
Opening Hours: Mon-Fri 9AM-6PM | Closed from Sat-Sun
21. Attila Cybertech

They strictly conform to the National Institute of Standards Technology (NIST) Framework for Critical Infrastructure Cybersecurity Improvement, which promotes its own cyber security framework. In contrast to the system security measures already in place, Attila Cybertech aims for the clear implementation of this model. Their operations are modernizing and merging fragmented legacy systems through broad base and productivity-enhancing facilities. Unlike the region’s traditional IT security companies, their industry expertise and knowledge in developing cyber security strategies makes them a unique competitor for the rest of the regions.
You will find a suitable approach for your organization with the company’s deep technical expertise in both Operational Technology (OT) and Information Technology (IT). In developing, conducting and enforcing cyber security standards and regulations in industrial control and automation systems, they have also been accredited to fulfill the requirements of International Standard, a testimony to their adherence. They seek to improve their approach through continuous research and innovation with input from their clients. To assure that only the approved solution that satisfies both Cyber Security and Functional Safety requirements is introduced, they continuously analyze the latest products.
Website: https://www.attilatech.com
Contact: +65 6747 6116
Location: 39 Ubi Road 1, #02-05, Singapore 408695
Opening Hours: Mon-Fri 8.30AM-5.30PM | Closed from Sat-Sun
22. Argentra Solutions

Data Loss Prevention (DLP) is a technique for organizations to stop users from sending non-authorized third parties’ private information. By delivering a confidential document to the wrong address, dropping a USB stick with classified information, or losing a confidential folder into the shared drive’s public directory, information can unintentionally be misplaced. Employees or managers can also take private information if they depart from the company. Argentra Solutions brings from the leading brands, this DLP solutions.
A Data Loss Prevention Platform (DLP) is a content-aware software capable of reading the messages and document content in-network, desktop, or in local or shared drives. The DLP system functions as an automated auditor who continuously reviews if confidential data is in the wrong location or being sent to the wrong party. To achieve a greater degree of document protection, most clients must incorporate their DLP authentication systems, Digital Rights Management (DRM). DLP and authentication have been identified as criteria in Section 9 of the current MAS Technology Risk Management (TRM) regulations. Argentra Solutions has various DLP strategies that suit different price ranges and security requirements from SMEs to large businesses.
Website: https://www.argentra.com
Contact: +65 6846 2393
Location: Performance Building, 158 Kallang Way, #07-01/02, Singapore 349245
Opening Hours: Mon-Fri 9AM-6PM | Closed from Sat-Sun
23. IT Solution

Irrespective of the size or sector of your organization, it is incredibly important to preserve data of your business and sensitive customer information, usually due to the growing number of instances of security breach over the decades. Infringement of information presents dangerous threats to your company and customers ‘ safety. It may be harmful to connect the private and sensitive data for unauthorized users. Your data can be manipulated and abused to scare your business credibility and integrity on the market and reduce the trust, your consumers had in your company.
It is essential to enforce the best and highest data protection measures to prevent unauthorized users and cybercriminals from breaching your valuable information and confidential business data. They are trained in data protection solutions at IT Solution. They can provide the most efficient solutions for data security, thus drastically reducing the risk of possible data compromises. You can be assured that your data will never be in the hands of the wrong people with them. Their solutions include Firewall, that can block all sorts of network-based cyber threats, actually protects your company from unauthorized users, cyber-attacks, spam, viral infections and spyware. Their Firewall product is rapid to launch and offers unparalleled data security for companies.
Website: https://www.itsolution.com.sg/it-services
Contact: +65 6690 3275
Location: 51 Goldhill Plaza, #07-07, Singapore 308900
Opening Hours: Mon-Fri 9AM-6PM | Closed from Sat-Sun
24. Assure IT

Assure IT is a company specializing in software development, risk management and regulation in Singapore. A holistic team includes seasoned senior government and business leaders spanning sectors including ICT, Security, Banking and Finance, Research and Development, and Manufacturing. Cybersecurity is a significant business threat. Assure IT adopts a systematic, robust cybersecurity system. When designing policies to tackle cyber security threats, they look at people, procedures, and technologies. Their approach to secure, track and react offers a comprehensive strategy to help our customers handle the risks of cybersecurity.
Through strategic planning to operational controls in the fields of policy, risk and regulation, they provide a wide range of cybersecurity and risk advisory services. IT assessments and evaluations of risk-based and enforcement standards are also included in their cyber security solutions. These can be conducted whether separately or in combination with a security review, financial audit, internal audit or other form of commitment to certification. Security screening can be conducted to find weaknesses in the systems and applications of your company. In pre-commissioning and routine safety testing criteria, they use a mix of automated systems and manual evaluation.
Website: https://www.assure-it.com.sg
Contact: +65 6638 9038
Location: 28 Genting Land, #08-07, Singapore 349585
Opening Hours: Mon-Fri 9AM-5.30PM | Closed from Sat-Sun
25. FireEye

Current cyber hackers are advanced, excellently-funded, very organized, and use highly targeted tactics that reveal security measures that are technology-only. Organisations need to know what people feel, how they function, and what they want in order to identify and avoid attackers. However the word security threat allows most people to think and stop feeding on risk. FireEye Threat Intelligence presents the security agency with a multi-layered approach to the use of intelligence.
Threat feeds are helpful, but to grasp its implications for your company, you also need the surrounding context as a signal. Tactical intelligence is great, but strategic intelligence is also required to understand what challenges you are facing and how to coordinate your defences to counter them. Operational intelligence is useful in reacting to an attack immediately, but you still need intelligence to enable you to switch from reactive to constructive risk detection efforts. You get all of this and more from FireEye Threat Intelligence. It’s the distinction between the company being told and an appliance being informed.
Website: https://www.fireeye.com
Contact: +65 3158 5588
Location: AXA Tower, 8 Shenton Way, #38-01, Singapore 068811
26. INStream

INStream helps companies address issues and challenges related to cyber security. They work together and supply a stable and efficient security environment capable of preventing and detecting cyber-attacks threatening businesses across all sectors around the globe. They provide creative end-to-end cybersecurity strategies and services to companies in Singapore and internationally, including database safety as well as urgent malware detection.
INStream offers the technical competence provided by its team of dedicated developers located in Singapore to efficiently evaluate the cybersecurity needs of businesses and develop innovative strategies to fulfill even the most demanding business objectives and goals. They aim to become a collaborator on which all organizations can rely on for efficient and reliable strategies. They remain alert, responsive and innovative as a one-stop shop for IT security products in Singapore to provide a full range of services designed to address crucial issues in cyberspace.
Website: https://www.instreamcorp.com
Contact: +65 6744 0794
Location: Yu Li Industrial Building, 37 Lorong 23 Geylang, #05-05, Singapore 388371
Opening Hours: Mon-Fri 9AM-6PM | Closed from Sat-Sun
27. NTT Security

When you weigh the consequences and positive impacts of digital transformation, evaluate how best to evolve and prosper in this rapidly changing environment and maintain your online security at the same time. The challenges are becoming increasingly complex, enticing as the benefits are, and to combat them requires solutions of equal complexity. The Web Security Services (WSS) of NTT Security is just such a solution that integrates the Web Security Services of Symantec with their real-time risk intelligence and evaluation to supply advanced and controlled threat detection and prevention solutions. As part of their Global Managed Security Services, the services are offered to customers around the world, guaranteeing that a high-quality product is accessible to everyone.
Through merging threat detection and building a network with defense capabilities, WSS defends against destructive security threats in real-time. Real-time network surveillance also needs a time and resources commitment that may not be accessible to your company, a need which is felt even more keenly as professional security experts are becoming more difficult to find. Their wide range of defensive capabilities, including crisis mitigation and effective security assessment, not to mention accessibility to their world-class professional security experts, helps you to focus on your business goals, secure in the knowledge of securing your information and assets.
Website: https://www.nttsecurity.com
Contact: +65 6493 7650
Location: Gateway West, 150 Beach Road, #21-00, Singapore 18972
28. ICD Security Solutions

ICD Security Solutions offers high performance, advanced security system deployment services throughout the Asia Pacific region. Operating with consumers from a variety of industries, they are acquainted in various verticals with the frequently encountered difficulties. They also work very closely with customers to recognize their particular needs, developing and implementing the optimal solution to satisfy their current requirements and plans for future development. They guarantee that the services are provided reliably and organized seamlessly, irrespective of where the project happens, from consumers with small, stand-alone sites to international companies with sites around the world.
They also provide an extensive system of maintenance services to insure that your sites run efficiently and that any problems are resolved in the shortest time possible, maximizing efficiency for your system. They take a constructive maintenance method, providing regular preventive maintenance reviews to detect and fix possible problems before they can become serious. Each customer service case is handled with detailed, structured documentation and reports given while properly following protocols and requirements. Not only does this keep you updated, but also systematically logs essential data to help us identify trends of system problems over time.
Website: https://www.icdsecurity.com
Contact: +65 6570 3973
Location: 114 Lavender Street, Singapore 338729
29. Security & Risk Solutions

Security & Risk Solutions aims to provide competent and comprehensive security solutions through an intelligence-driven team as the leading security firm in the country. They aspire to be the industry leader in the security sector in the region and pledge to provide their customers with a steadfast commitment to quality in delivering professional security services. Technology innovation has generated huge economic opportunities and the standard of living has significantly improved.
There will always be two sides to each coin, but large quantities of data will have to be guarded with the rise of technology. Information has turned into the new gold. Their group of technical experts at Security & Risk Solutions Cybernetics will assist their clients in identifying, evaluating, minimizing and managing threats through some of the most effective cybersecurity system. They will continue to promote and maintain a philosophy of lifelong learning that supports technological advances. They will constantly supply their security workers with a safe working atmosphere through their dedication and commitment and grow them into better leaders.
Website: https://security-risksolutions.com
Contact: +65 6747 2832
Location: GEMINI@SIMS, 2 Sims Close, #06-07, Singapore 387298
Opening Hours: Mon-Fri 9AM-6PM | Closed from Sat-Sun
30. Imperva

Imperva Data Activity Monitoring (DAM) establishes and enforces a consistent cloud-wide and on-site data security and enforcement framework. Get a single glass control board spanning relational databases, mainframes, large data networks, information centers, and company file stores. Alert yourself to malicious activity of entry. Dynamic profiling automatically generates a whitelist of information items that individual server accounts routinely access. Develop policies that warn or restrict access whenever a profiled user tries to access a non-whitelisted data entity.
Imperva DAM combines with Data Risk Analytics, which uses machine learning and group evaluation to create a functional situational model of typical user access to database servers. In order to find sensitive information or secret bugs, their methods can be applied immediately to prevent server attack threats through predefined security policies and automated discovery. This checks for protocol and OS level threats and assaults, as well as unauthorized SQL operation, then warns quarantines and blocks unauthorized data protection activities where necessary.
Website: https://www.imperva.com
Contact: +65 6835 7104
Location: Suntec Tower 1, 7 Temasek Boulevard, #15-01, 038987
31. LogRhythm

If your team struggles with limited resources, you are possibly faced with reaction times that are longer than optimal. This jeopardizes the company. Security orchestration, automation, and response (SOAR) can help. This streamlines workflows and speeds up screening, researching and reacting to threats. SOAR makes the work of your team quicker and easier. With the SmartResponse from LogRhythm, you are capable of deciding the optimal solution to optimize work so that your team can concentrate on a nuanced response to incidents that needs creativity and skill.
Pick from fully autonomous blueprint responses or semi-automated, endorsement-based response actions that enable users to evaluate before executing counter measures. If there is no centralized location for your team to communicate or dig through past reports, accidents may slip under the radar. In an examination with Case Management, LogRhythm makes it much easier for your team to establish and monitor remediation and restoration. An analyst can quickly escalate an incident, mark it as a concern, and appoint an employee. With these security instrumentation tools, your team should be able to consolidate all relevant case proof for final resolution and ease of access in the future in LogRhythm’s evidence locker database.
Website: https://logrhythm.com
Contact: +65 6222 8110
Location: 2 Peck Seah Street, Singapore 079305
Opening Hours: Mon-Fri 7AM-6PM | Closed from Sat-Sun
32. Vector InfoTech

Vector InfoTech provides communications systems and services that are designed to fulfill the real-world’s realistic requirements. They are committed to individual customer satisfaction, competence in all facets of their activities, and the delivery of technologically superior data processing and management systems. The organization has one overarching focus when addressing the project of each client in delivering inexpensive, efficient systems that allow customers to meet their key business objectives.
Vector InfoTech is committed to providing our customers with “Complete Solution” for their communications system specifications as well as incorporation of more dynamic system projects and data communication issues troubleshooting. The Industrial Data Communications solution portfolio of Vector InfoTech comprises of rugged models that are often needed in commercial settings. Solutions capable of handling a multitude of data sizes and communication distances allowing for a seamless and efficient flow of communication between devices.
Website: http://www.vectorinfotech.com
Contact: +65 6356 7333
Location: 3015A Ubi Road 1, #05-13, Singapore 408705
Opening Hours: Mon-Fri 9AM-6PM | Closed on Sat-Sun
33. PTC

They give their clients the most innovative solutions. Their key purpose is to help and assist our clients. For contrast, they’ll find all the various technologies. The understand that their clients need committed IT delivery and supporting tools. Their group is approachable and are considerate about the various business environments. Their team consists of the Account Manager, Systems Architect, Project Manager and the Production Management team to ensure that each project is successfully applied to their client. They guarantee that their research is communicated transparently and their staff members are empowered to achieve the best quality to satisfy customer requirements.
They have built a security product portfolio in PTC that can enable businesses to win the battle against hackers and cybercriminals to impede their business. CylanceProtect is an AI-based lightweight, high-performance EPP, not reliant on regular signature changes, or cloud intelligence which requires internet connection to efficiently prosecute high-efficiency malware compared to conventional AV companies. CylanceOptics is an EDR tool that helps the internal security team examine efficiently, acquire forensics, conduct risk tracking, detect the source, and cure if compromised.
Website: http://ptcsys.com
Contact: +65 6282 0255
Location: 29 Tai Seng Street, Singapore 534120
Opening Hours: Mon-Fri 9AM-6PM | Closed from Sat-Sun
34. InsiderSecurity

To scan for threats in your system, Monitor uses predictive formulas and cybersecurity behavior analytics. They enabled their clients to effectively spot a number of sneaky cyberattacks that often go undetected. Utilizing sophisticated Monitor Sensors offers the greater visibility needed to secure the channel’s intelligent attackers. Control sensors can even prevent the cyber infringement in real time. Monitor is designed for running in the network or on-site. Monitor Sensors transmit data encoded to the cloud for cloud delivery, and the data of each consumer is handled in their own stable, segregated silo.
Perpetrators nowadays constantly break the boundaries of the network to get inside the system. When attackers establish a foothold into your system, they reach higher-value targets such as your servers, or “pivot.” It’s not enough for firewalls and anti-virus to track and avoid such attacks. InsiderSecurity Monitor uses detectors in important parts of your system, as well as advanced sophisticated software to identify hackers within the system.
Website: https://insidersecurity.co
Contact: +65 6270 4029
Location: 81 Ayer Rajah Crescent, #03-48, Singapore 139967
Opening Hours: Mon-Fri 9AM-6PM | Closed from Sat-Sun
35. CSIntelligence

From harmless pranks to converting the machines of your company into “zombies” to carry out attacks on many other organisations. Throughout the years, malware has learned to take many forms. It can be as easy as receiving an email attachment or viewing a website to get corrupted with malware or a virus. Fallen victim to an assault on malware could result in the loss of sensitive and critical information that could jeopardize the business operations of your company. Instead of responding to malware threats, secure yourself with proactive protection against malware by intercepting and preventing the assault before it does any harm with their services to your company.
Current protection techniques presume that by installing a protective barrier or wall, it is possible to prevent hackers from breaching the networks. But, when criminals often figure out new ways and techniques, security threats can already bypass these obsolete conventional technologies. Legacy SOC controls only firewall boundary logs, network-based security systems, and databases. It indicates they do not have the ability to understand why, where and precisely what contributed to the whole story. On the other hand, CSIntelligence can provide you with complete details of any risk or intrusion by conducting in-depth analyzes and rapid identification of threats like zero-day threats by having the appropriate expertise and software.
Website: https://www.csintelligence.asia
Contact: +65 6407 1341
Location: Suntec Tower 2, 9 Temasek Boulevard, #09-01, Singapore 038989
Opening Hours: Mon-Fri 8.30AM-6PM | Closed fromSat-Sun
36. Trend Micro

Today, virtually all companies claim to defend you against visible and invisible risks, but they don’t have access to the hidden weaknesses within the network. By good convergence of intrusion detection solutions (IPS) and enhanced threat security , Trend Micro offers an evocative combination of cross-generation strategies and sophisticated malware detection to optimize the safety that go beyond what is known and unknown. With the network defense of Trend Micro, you will accomplish quicker time to defend against established, unknown and unrevealed threats, optimize your security infrastructure with high efficiency and automated protection which suits your hybrid setting.
Furthermore, with real-time exchange of risk information, unified threat analysis, and automated restoration, you can prioritize and react towards the most urgent threats. Through their cybersecurity solutions, in real-time with proprietary machine learning, you can identify and avoid new threats affiliated through known malware groups and unidentified in-line malware. Trend Micro assures that award-winning solution is given to provide you with best possible security for your setting.
Website: https://www.trendmicro.com/en_sg/business.html
Contact: +65 6379 2060
Location: Suntec Tower Four, 6 Temasek Boulevard, #16-01 to 05, Singapore 038986
37. ST Engineering

IT, operational software and Internet-of-Things (IoT) should improve computer and internet connectivity. Complex networks will integrate further to address new opportunities in business and in the modern digital world. That, in turn, would make the bolstering of these different cyber-attack surfaces more complicated. Defenders of cybersecurity will experience arduous obstacles in safeguarding these networks for the coming years. The response to this would be to follow the appropriate framework for cybersecurity. ST Engineering is dedicated to providing its clients with cyber-secure communications systems. Cybersecurity must be an essential part of the structure of any device or network. Technology is being used to cut down the noise level by removing 90 percent of foreseen threats. Thereafter, systems and skills are being used to cope with yet another 9% of advanced risks and malware. They then use their broad knowledge to remove the very last 1% of advanced and unidentified risks.
A prominent supplier of reliable and creative cybersecurity services, they have nearly twenty years of profound experience and strong track record in securing and preserving key infrastructure. They plan, develop, prepare and run cybersecurity operations centers for their clients through their network of qualified cybersecurity specialists. They have comprehensive cyber-secure services and products in encryption, software technology, auditing, and enforcement with their extensive expertise and experience. They also heavily invested in researching and developing, actively participating in top research organisations, educational associates, and industry experts in the construction of capabilities to generate future-ready cybersecurity approaches and stay on top against cyber assailants.
Website: https://www.stengg.com/cybersecurity
Contact: +65 6722 1818
Location: Electronics Park Road, 1 Ang Mo Kio, #07-01, Singapore 567710
Opening Hours: Mon-Fri 8AM-5.30PM | Closed from Sat-Sun
38. Ace Pacific Group

ACE Pacific Group strives to be your preferred distributor of cybersecurity solutions in the Asia Pacific region. They offer cyber security and analytical services that enables the company to succeed through using state-of-the-art technology patterns to enhance economic performance and optimize daily operations for both you and your customers. They have established themselves as a value-added one-stop cybersecurity solutions provider to constantly meet the ever-changing cybersecurity landscape on the Asia Pacific market and even on a global scale.
They have developed the expertise to facilitate this exchange and they can provide the most pressing business, technology, strategy and culture concerns of an organization with innovative security solutions. They have successfully helped many clients to maximize productivity, efficiency, overall performance of their encrypted network and protect their confidential data from cyber attacks. Their partners, includes statutory boards, government bodies, financial institutions, banks, MNCs and SMEs.
Website: http://ace-pac.com
Contact: +65 6513 0018
Location: Kewalram House, 8 Jalan Kilang Timor, #04-15/16, Singapore 159305
Opening Hours: Mon-Fri 9AM-6PM | Closed from Sat-Sun
39. Secureage Technology

SecureAge Technology is a data security company headquartered in Singapore, putting real security and usability on an equal footing. Their history is one of protecting data from the most advanced and persistent cyber threats from government and business. The user-centered and simple solutions derived from the philosophy of SecureAge offer clarity and calm in the most complex security environments. Patented technologies provide complete data protection and use advanced encryption techniques. Their team brings unprecedented expertise, ingenuity and passion for data security to make this possible. Today, they aspire to provide the highest level of data security for everyone and continue to develop innovative solutions.
Some infringements of information are either related to deliberate or accidental insider behavior, or are detected during delivery. SecureAge SecureData offers clear and automated file and folder cryptography at the beginning of individual files without user consideration, action, or even awareness.Intrinsic and Undetectable PKI encryption prevents information from leakage, loss, or getting stolen. In addition, enhanced whitelisting and software linking functions tackle all malware, ransomware, zero-day attacks and sophisticated malicious risks which might contribute to privacy breaches in the first place.
Website: https://www.secureage.com
Contact: +65 6873 3710
Location: 3 Fusionopolis Way, Singapore 138633
Opening Hours: Mon-Fri 9AM-6PM | Closed from Sat-Sun
40. CyberQuote

As one of the leading cyber security service providers in Singapore and other regions across the world, CyberQuote has a proven reputation for its excellent service and endeavours to build long-term relationships with their customers and business partners. With over 20 years of experience in serving the public and the financial services industry, CyberQuote specialises in financial training and information technology solutions including securities trading and processing systems.
At CyberQuote, they run a 4-step Cyber Safeguard Awareness Programme that is tailored to help raise the overall IT security awareness level in your organisation. There is also a vulnerability assessment to identify possible vulnerabilities that pose cyber security threats, and penetration testing can be conducted to patch and seal any security gaps to protect against hackers. If you want to beef up your security protection, their Cyber Hygiene Manager offers innovative solutions like Network Access Control (NAC) to enhance your network security enforcement and defence.
Website: https://cyberquote.com/sg/cyber-security-and-data
Contact: +65 6505 0199
Location: Grand Building, 17 Phillip Street, #02-00, Singapore 048695
Opening Hours: Mon-Fri 9AM-6PM | Closed on Sat & Sun